CVE-2026-23744: Your MCP Discovery Pipeline Is an Attack Surface
Algis Dumbris • 2026/03/23
The Tool You Use to Find Tools Just Became the Weapon
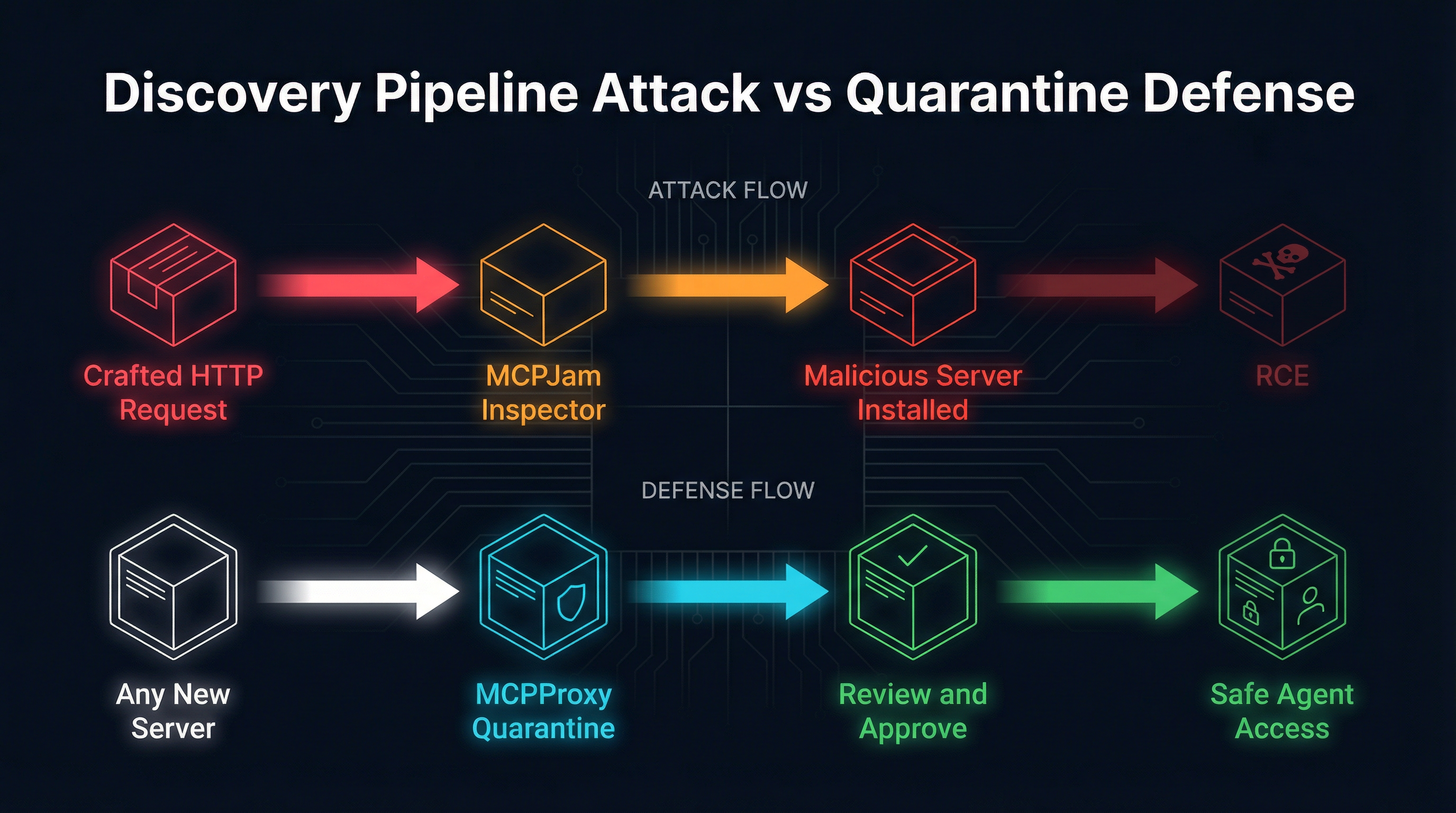
When we talk about MCP security, we talk about malicious servers, prompt injection, tool poisoning, and config file attacks. We focus on what happens after a server is installed and running. CVE-2026-23744 breaks that assumption entirely.
The vulnerability is not in an MCP server. It is in MCPJam Inspector — a popular discovery and testing tool that developers use to browse, evaluate, and install MCP servers. A single crafted HTTP request to MCPJam Inspector triggers the installation of a malicious MCP server on the developer’s machine and achieves full remote code execution. No user interaction beyond visiting a page. No confirmation dialog. No install prompt.
The attack surface is not your tools. It is the mechanism by which you find and install tools.
This is a new attack class. And it demands a fundamentally different defense posture — one where every server installation, regardless of source, passes through a quarantine gate before it can reach an agent.
Inside CVE-2026-23744: How a Discovery Tool Becomes an Installer for Malware
MCPJam Inspector is designed to help developers explore MCP servers. You point it at a registry, browse available servers, test tool calls, and install servers into your local environment. It is the “app store” experience for the MCP ecosystem — a graphical interface that simplifies the process of adding new capabilities to your AI development workflow.
The vulnerability exploits how MCPJam Inspector handles incoming HTTP requests during its local server browsing session. An attacker crafts a request that abuses Inspector’s server-installation API endpoint. Because Inspector runs with the developer’s local permissions and has the ability to modify MCP configurations, the crafted request triggers the following chain:
-
Crafted HTTP request reaches MCPJam Inspector’s local HTTP interface. This can happen through a malicious link, a compromised web page, or a cross-site request from any browser tab the developer has open.
-
Inspector processes the request as a legitimate server installation command. The request contains a server definition pointing to an attacker-controlled MCP server package.
-
The malicious server is installed into the developer’s MCP configuration. Inspector writes the server entry to the local config, and the server process starts with the developer’s full permissions.
-
Remote code execution is achieved. The malicious server runs arbitrary commands, exfiltrates credentials, or establishes persistence — all under the guise of a legitimate MCP server that the developer never explicitly chose to install.
The attack requires no credentials, no authentication bypass, and no exploit of a memory corruption bug. It uses the tool’s own intended functionality — installing MCP servers — against the developer. The only thing the attacker needs is for the developer to have MCPJam Inspector running while they visit a page the attacker controls.
Why Discovery Pipeline Attacks Are a New Class
The MCP security community has been focused on three categories of attack:
Server-side vulnerabilities — bugs in running MCP servers that allow SSRF, command injection, or data exfiltration. The 30+ CVEs catalogued through early 2026 mostly fall here.
Configuration injection — attacks like MCPwned where an attacker modifies config files to add malicious server definitions. The developer runs their editor, the config is parsed, and the malicious server starts.
Prompt injection and tool poisoning — attacks where a running server manipulates the AI agent through crafted responses, hidden instructions, or misleading tool descriptions.
CVE-2026-23744 does not fit any of these categories. It targets the discovery and evaluation phase — the moment before the developer has decided to install anything. The developer is browsing. They are evaluating. They have not committed to trusting any particular server. And yet the attack achieves installation and execution.
This is structurally different for three reasons:
1. It subverts the trust decision itself. Configuration injection attacks assume the developer will eventually load a config file. Prompt injection assumes a server is already connected. Discovery pipeline attacks bypass the decision entirely. The developer never chose to install the malicious server. Their discovery tool made that choice for them.
2. It weaponizes the security review process. MCPJam Inspector exists to help developers make informed decisions about which servers to trust. Attacking the inspector tool means the very act of being careful — of evaluating servers before installing them — becomes the attack vector. The more security-conscious the developer, the more likely they are to use an inspector tool, and the more exposed they become.
3. It scales through registries. Discovery tools connect to registries. Registries list hundreds or thousands of servers. If the discovery tool itself is compromised, every server in every registry becomes a potential delivery mechanism. The attacker does not need to publish a malicious package. They just need to get their crafted request to any developer running the vulnerable inspector.
This is the supply chain attack moved one layer upstream. We spent the last year securing the servers themselves. CVE-2026-23744 shows that the pipeline through which developers find those servers is equally critical.
The Quarantine-First Defense
If you cannot trust the mechanism that installs servers, you need a gate that catches everything that arrives — regardless of how it got there.
This is what quarantine-first architecture provides. MCPProxy implements quarantine as the default state for every new MCP server connection. There is no path from “installed” to “active” that does not pass through explicit human review.
Here is how it neutralizes the CVE-2026-23744 attack chain:
Step 1: The malicious server is installed. Whether through MCPJam Inspector’s vulnerability, a compromised config file, or any other installation mechanism, the server definition arrives in the system. This step is the one we cannot always prevent — there will always be new installation vectors, new discovery tools, new ways for server definitions to appear.
Step 2: MCPProxy intercepts the connection. When the newly installed server attempts to register its tools with the MCP ecosystem, MCPProxy catches it. The server is placed in quarantine. Its tools are catalogued but not exposed to any agent.
Step 3: The operator reviews. The quarantined server appears in the pending list. The operator examines the server’s declared tools, checks the package provenance, and makes an informed decision:
mcpproxy upstream list # Shows all servers including quarantined ones
mcpproxy upstream approve <name> # Explicitly approve after reviewStep 4: Only approved servers reach agents. Until the operator runs upstream approve, the malicious server’s tools are invisible to every agent in the system. The attacker achieved installation but not execution. The blast radius is zero.
This defense works regardless of the installation vector. It does not matter whether the server arrived through CVE-2026-23744, a compromised config file, a malicious npm package, or a social engineering attack. The quarantine gate is the same for all of them.
What Quarantine-First Architecture Actually Means
“Quarantine by default” is a specific architectural commitment, not a marketing phrase. It means:
Every new upstream server starts untrusted. When you add a server to MCPProxy, it enters quarantine automatically:
mcpproxy upstream add my-new-server --stdio "npx -y @example/mcp-tools"
# Server is added in QUARANTINE state -- tools are not available to agentsThere is no flag to skip quarantine. There is no “trusted source” list that auto-approves servers. The assumption is that any new server, from any source, might be malicious — because CVE-2026-23744 proves that even servers you did not choose to install can appear in your configuration.
Tool inventories are analyzed before exposure. While a server is quarantined, MCPProxy catalogues its tools — names, descriptions, input schemas. This inventory is available for review but is never presented to an agent as an available capability. If a quarantined server declares a tool called read_file that takes a path parameter with suspiciously broad permissions, the operator sees this during review and can reject it.
Approval is explicit and auditable. Every transition from quarantine to active is a deliberate operator action. MCPProxy logs these transitions, creating an audit trail of exactly which servers were approved, when, and by whom. If a compromised server slips through, the audit trail shows exactly when it was approved and what its tool inventory looked like at approval time.
Re-quarantine on change. If an approved server’s tool inventory changes — new tools appear, existing tools change their descriptions or schemas — MCPProxy can flag the change for re-review. This addresses the “rug pull” scenario where a server is benign at approval time but later updates to include malicious tools.
Protecting Your Discovery Workflow: A Practical Guide
CVE-2026-23744 means that discovery tools are part of your attack surface. Here is how to protect your workflow today.
Route Everything Through MCPProxy
Instead of letting discovery tools install servers directly into your MCP configuration, route all server management through MCPProxy:
# Install MCPProxy
go install github.com/smart-mcp-proxy/mcpproxy-go/cmd/mcpproxy@latest
# Start the gateway
mcpproxy serve
# Add servers explicitly -- they enter quarantine by default
mcpproxy upstream add filesystem --stdio "npx -y @modelcontextprotocol/server-filesystem /workspace"
mcpproxy upstream add github --stdio "npx -y @modelcontextprotocol/server-github"
# Review what is pending
mcpproxy upstream list
# Approve only after review
mcpproxy upstream approve filesystem
mcpproxy upstream approve githubYour AI assistant connects to MCPProxy, not to individual servers. MCPProxy routes tool calls to the appropriate upstream server. If a malicious server somehow appears in the configuration (via CVE-2026-23744 or any other vector), it sits in quarantine until you explicitly approve it.
Isolate Discovery Tools
If you use MCPJam Inspector or similar tools, run them in an isolated environment:
- Use a separate browser profile with no authenticated sessions to your MCP development environment.
- Run discovery tools in a container where they cannot modify your host’s MCP configuration files.
- Network-isolate the discovery environment so that even if a malicious server is installed in the container, it cannot reach your development network.
Audit Your Current Server Inventory
Before adding quarantine protection, audit what is already installed:
# List all currently configured servers
mcpproxy upstream list
# Check for servers you do not recognize
# Any server you did not explicitly add should be investigatedIf you find servers you do not recognize, investigate their origin. They may have been installed by a compromised discovery tool, a malicious config file in a cloned repository, or an automatic update that pulled in a new dependency.
Monitor for Configuration Changes
The most dangerous aspect of CVE-2026-23744 is that it modifies your configuration silently. Set up monitoring on your MCP configuration files:
- Watch
~/.mcpproxy/mcp_config.jsonand similar files for unexpected modifications. - Use git to track configuration changes and review diffs before they take effect.
- In team environments, require pull request review for any changes to shared MCP configurations.
The Attack Surface Map Has Expanded
Before CVE-2026-23744, the MCP attack surface map looked like this:
- Config files — attacker writes a malicious server definition.
- Running servers — attacker exploits a vulnerability in a server.
- Protocol channel — attacker injects malicious content through tool responses.
After CVE-2026-23744, the map includes:
- Discovery tools — attacker exploits the tool used to find and evaluate servers.
- Registry interactions — attacker uses the browsing/evaluation process itself as an attack vector.
- Installation APIs — attacker targets the automated mechanisms that translate “I want this server” into “this server is now running.”
Each of these new vectors shares a common property: they occur before the developer has made a trust decision. Traditional security controls — approval workflows, capability restrictions, sandboxing — all assume the trust decision has already happened. They protect the execution phase. They do not protect the installation phase.
Quarantine-first architecture is the only approach that covers both. By intercepting at the boundary between installation and execution, it creates a hard gate that applies regardless of how the server arrived. The developer’s trust decision happens at the quarantine gate, not at the moment of installation. Even if the installation mechanism is compromised, the trust gate remains intact.
The Discovery Pipeline Is Infrastructure
We treat build pipelines as infrastructure. We audit our CI/CD systems, lock down our artifact registries, and verify the provenance of every dependency. We do this because we learned — through incidents like SolarWinds, Codecov, and the xz backdoor — that the pipeline is as critical as the code it delivers.
CVE-2026-23744 is the MCP ecosystem’s equivalent lesson. The discovery pipeline — the tools, registries, and workflows that developers use to find and install MCP servers — is infrastructure. It deserves the same rigor we apply to build pipelines.
This means:
- Discovery tools must be patched and updated with the same urgency as production servers. MCPJam Inspector users should update immediately.
- Registry interactions should be authenticated and logged, not anonymous browsing sessions on a local HTTP server.
- Installation must be a separate, gated step from discovery. Browsing a registry should never result in an installed server.
- Every installation, regardless of source, should pass through quarantine. This is the single most effective control.
The MCP ecosystem is young enough to build these defenses before the pattern hardens. We do not need to repeat the multi-year remediation cycles that npm, Docker, and GitHub Actions went through. The architectural answer is known: separate discovery from installation, separate installation from execution, and put a quarantine gate at every boundary.
Your MCP servers might be secure. Your configuration files might be locked down. But if the tool you use to find those servers is compromised, none of that matters. The attack surface is not where you think it is. It is one layer upstream — in the discovery pipeline itself.
Quarantine everything. Trust nothing until reviewed. The pipeline is the perimeter.