CVE-2026-27896: How Go's JSON Parsing Nearly Broke MCP Security
Algis Dumbris • 2026/03/20
On March 1, 2026, a vulnerability disclosure dropped that should have set off alarms across the MCP ecosystem. CVE-2026-27896 — a case-sensitivity bypass in the official MCP Go SDK — earned a CVSS score of 9.1 (Critical). The attack is elegant in its simplicity: send a JSON-RPC request with "Method" instead of "method", and Go’s standard library happily parses it as if nothing is wrong. Your WAF, your security proxy, your request validator? They are all looking for the lowercase version. The capitalized variant sails right through.
This is not a theoretical concern. It is a proof-of-concept-available, actively-scoreable vulnerability that affects every MCP implementation built on the official modelcontextprotocol/go-sdk prior to version 1.3.1. And it arrives in the middle of what can only be described as an MCP security crisis: 30 CVEs and counting in barely 15 months since the protocol launched.
Here is what happened, how the attack works, whether MCPProxy is affected, and what you need to do about it.
The Vulnerability: Case-Insensitive Chaos
Go’s encoding/json package has a well-documented behavior that most Go developers know about but rarely think about in security terms: struct field matching is case-insensitive by default. When you define a struct with a field tagged json:"method", Go’s unmarshaler will happily match "method", "Method", "METHOD", and even "mEtHoD". They all resolve to the same struct field.
This behavior extends even further. Go’s JSON decoder also supports Unicode case folding, meaning that exotic characters like ſ (U+017F, Latin Small Letter Long S) can match their ASCII equivalents. A field name containing Unicode lookalikes can bypass string-level inspection while still parsing correctly at the application layer.
For most Go applications, this is a convenience feature. For security-critical JSON-RPC processing, it is a vulnerability.
JSON-RPC 2.0 specifies exact field names: method, params, id, jsonrpc. These are lowercase, period. Any security intermediary — a WAF, a reverse proxy, an MCP gateway — that inspects JSON-RPC traffic looks for these exact field names when applying security rules. If your firewall rule says “block requests where method equals tools/call and the tool name matches a blacklist,” an attacker simply sends "Method": "tools/call" instead. The WAF sees no method field and passes the request through. The Go SDK’s JSON decoder sees Method, matches it to the method struct field, and processes the request as intended.
Bypass achieved.
// What the attacker sends:
{
"jsonrpc": "2.0",
"Method": "tools/call",
"id": 1,
"params": {
"name": "execute_command",
"arguments": {"command": "cat /etc/passwd"}
}
}
// What the WAF sees: no "method" field → PASS
// What Go's json.Unmarshal sees: "Method" matches "method" → EXECUTE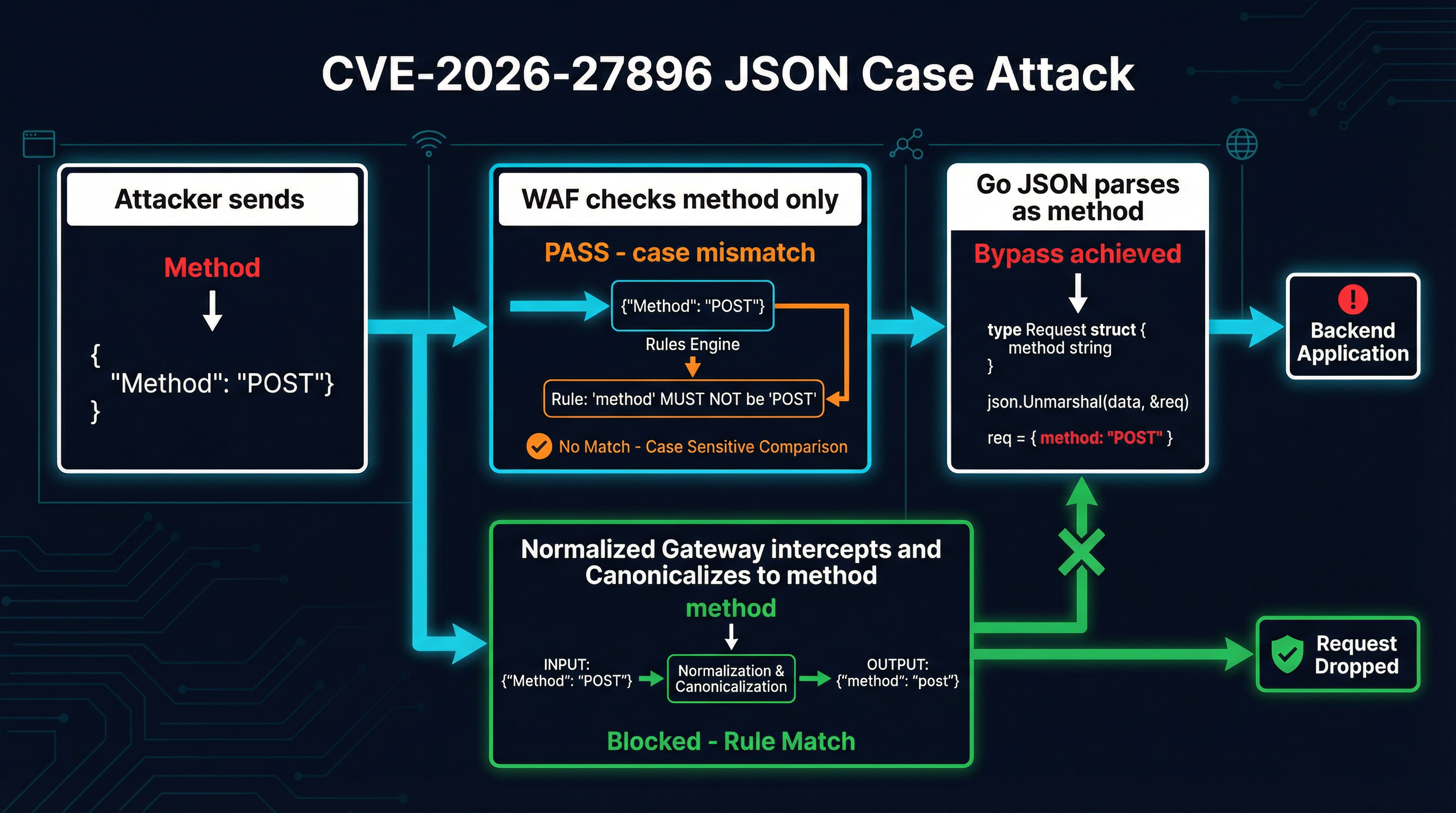
The vulnerability is classified under two CWEs: CWE-178 (Improper Handling of Case Sensitivity) and CWE-436 (Interpretation Conflict). The interpretation conflict framing is the important one. This is not a bug in Go’s JSON library — it is working as designed. The bug is in the assumption that the JSON producer and every intermediary in the chain will use the same case conventions. When they do not, the semantic gap between “what the security layer sees” and “what the application processes” becomes an attack surface.
Why This Matters for MCP: 30 CVEs in 15 Months
CVE-2026-27896 does not exist in isolation. It is one data point in a rapidly accelerating trend. The MCP ecosystem has accumulated 30 CVEs since the protocol launched in late 2024, with the discovery rate accelerating sharply: roughly 5 CVEs in the first half of 2025, 10 in the second half, and 15 in Q1 2026 alone. Half of all MCP vulnerabilities have been discovered in the last three months.
The attack surface splits into three layers:
Server-level vulnerabilities. 36% of MCP servers operate without any authentication. They accept connections from any client and execute any tool call without verifying identity. This is the low-hanging fruit — no CVE needed, just connect and call.
SDK-level vulnerabilities. This is where CVE-2026-27896 lives. Protocol implementation bugs in the official TypeScript, Python, and Go SDKs have a blast radius proportional to their adoption. One flaw in the Go SDK affects every Go-based MCP server and client that depends on it.
Host-level vulnerabilities. Tool calls execute with the permissions of the host process. Most MCP implementations have no mechanism for restricting which tools an agent can invoke, what filesystem paths a tool can access, or what network connections it can make. A compromised tool call inherits everything.
The JSON case sensitivity bypass is particularly dangerous because it targets the security intermediary layer — the WAFs, gateways, and proxies that organizations deploy specifically to compensate for server-level and host-level weaknesses. If your defense-in-depth strategy relies on a gateway normalizing and inspecting JSON-RPC traffic, CVE-2026-27896 undermines that entire layer.
MCPProxy’s Exposure: Not Directly Affected, But Lessons Apply
The first question after any CVE disclosure: are we affected?
MCPProxy uses github.com/mark3labs/mcp-go (currently at v0.44.0-beta.2), not the official github.com/modelcontextprotocol/go-sdk that CVE-2026-27896 targets. These are separate codebases with independent JSON parsing implementations. The mark3labs/mcp-go library has been the Go community’s primary MCP SDK since before the official SDK existed, and MCPProxy has used it since inception.
That said, mcp-go is also written in Go and also uses encoding/json under the hood. The same case-insensitive parsing behavior exists. The critical question is whether any security-sensitive code path depends on case-sensitive field name matching.
MCPProxy’s architecture provides structural protection here through several layers:
Tool-level routing, not field-level inspection. MCPProxy’s security model does not rely on inspecting the method field of incoming JSON-RPC requests to make authorization decisions. Instead, it operates at a higher abstraction level: BM25 tool discovery controls which tools are visible to agents, quarantine holds untrusted server schemas for review, and Docker isolation enforces OS-level boundaries on server processes. None of these mechanisms parse raw JSON-RPC method names for security decisions.
The mcp-go library handles JSON-RPC framing. MCPProxy delegates JSON-RPC message parsing entirely to the mcp-go library’s server implementation (mcpserver.MCPServer). MCPProxy registers tool handlers as Go functions — it does not manually inspect JSON-RPC request fields. This means the case-sensitivity behavior, while present in the underlying JSON decoder, does not create a bypass opportunity because MCPProxy does not have case-sensitive matching rules to bypass.
No WAF-style request filtering. MCPProxy is not a transparent proxy that inspects and filters JSON-RPC traffic based on field values. It is an MCP server that aggregates upstream tools and re-exposes them through its own MCP interface. Incoming requests are handled by mcp-go’s server framework, which routes to registered handlers based on method registration, not string matching against raw JSON.
However, this does not mean MCPProxy can ignore the issue entirely. The mark3labs/mcp-go library should adopt the same fix as the official SDK: enforce case-sensitive JSON parsing via dec.DontMatchCaseInsensitiveStructFields() (available in Go 1.24+). Any downstream tool that receives JSON payloads through MCPProxy and processes them with encoding/json inherits the case-sensitivity behavior. Defense in depth means fixing the behavior everywhere, even when no current exploit path exists.
The Fix: What Changed in go-sdk v1.3.1
The official MCP Go SDK fixed CVE-2026-27896 in version 1.3.1 by enforcing case-sensitive JSON parsing. The key change replaces standard json.Unmarshal behavior with explicit decoder configuration:
dec := json.NewDecoder(bytes.NewReader(data))
dec.DontMatchCaseInsensitiveStructFields()
err := dec.Decode(&request)The DontMatchCaseInsensitiveStructFields() method, introduced in Go 1.24, tells the decoder to only match JSON field names that exactly match the struct tag or the exported field name. With this setting, "Method" no longer matches a field tagged json:"method" — the request is rejected or the field is ignored.
For projects that cannot immediately upgrade to Go 1.24, there are alternative defensive patterns:
Pre-validation with strict parsing. Before passing JSON to your application logic, validate that all JSON-RPC field names match the expected case:
func validateJSONRPCFieldCase(data []byte) error {
var raw map[string]json.RawMessage
if err := json.Unmarshal(data, &raw); err != nil {
return err
}
allowed := map[string]bool{
"jsonrpc": true, "method": true,
"params": true, "id": true,
"result": true, "error": true,
}
for key := range raw {
if !allowed[key] {
// Check if it's a case variant of an allowed key
if allowed[strings.ToLower(key)] {
return fmt.Errorf(
"rejected case variant %q (expected lowercase)",
key,
)
}
}
}
return nil
}Request normalization at the gateway. If you operate an MCP gateway or proxy, canonicalize all JSON-RPC field names to lowercase before passing requests to backend handlers. This eliminates the semantic gap regardless of what the backend’s JSON decoder does:
func normalizeJSONRPCFields(data []byte) ([]byte, error) {
var raw map[string]json.RawMessage
if err := json.Unmarshal(data, &raw); err != nil {
return nil, err
}
normalized := make(map[string]json.RawMessage)
for key, value := range raw {
normalized[strings.ToLower(key)] = value
}
return json.Marshal(normalized)
}These are stopgap measures. The correct long-term fix is upgrading to Go 1.24+ and using DontMatchCaseInsensitiveStructFields() in every JSON decoder that processes untrusted input.
Broader Lessons: Every MCP Gateway Needs Request Normalization
CVE-2026-27896 is a specific instance of a general problem: interpretation conflicts between security intermediaries and application backends. This class of vulnerability has been exploited in HTTP (request smuggling via header case), SQL (case folding in identifiers), and now JSON-RPC. Wherever two systems parse the same data with different rules, an attacker can craft input that means one thing to the security layer and another to the application.
For MCP specifically, this means every gateway, proxy, and security intermediary needs to do more than just inspect traffic. It needs to normalize traffic before inspection. The normalization checklist for MCP JSON-RPC:
-
Field name canonicalization. All JSON-RPC field names must be lowercased before any security rule evaluation. This closes CVE-2026-27896 and all future case-variant bypasses.
-
Unicode normalization. Apply NFKC normalization to all string values, including field names and tool names. This prevents homoglyph attacks where
tooIs/call(with a capital I) passes a filter looking fortools/call. -
Duplicate field handling. JSON technically allows duplicate keys. If a request contains both
"method": "safe/operation"and"method": "dangerous/operation", which one wins? Go’sencoding/jsontakes the last value. Your security filter might check the first. Reject requests with duplicate JSON-RPC fields entirely. -
Schema pinning. Tools like MCPDome compute SHA-256 hashes of tool definitions and block servers that modify their schemas after registration. This prevents a class of attack where a server initially presents benign descriptions and later swaps in malicious ones — an attack that no amount of JSON normalization can catch.
-
Defense in depth beyond the wire. MCPProxy’s architecture demonstrates why wire-level inspection alone is insufficient. BM25 tool discovery limits the attack surface by controlling which tools reach agents. Quarantine holds untrusted schemas for analysis before they enter the tool pool. Docker isolation enforces OS-level boundaries that persist even if JSON-RPC-level defenses fail. No single layer is sufficient; you need all of them.
What You Should Do Now
If you use the official MCP Go SDK (modelcontextprotocol/go-sdk): Upgrade to v1.3.1 or later immediately. This is a critical-severity vulnerability with a proof of concept available.
go get github.com/modelcontextprotocol/go-sdk@v1.3.1If you use mark3labs/mcp-go: You are not directly affected by this CVE, but audit your codebase for any security logic that depends on case-sensitive JSON field matching. Consider adding request normalization at your ingress points.
If you operate an MCP gateway or proxy: Add JSON field name canonicalization to your request pipeline. Do not assume that upstream clients will send correctly-cased field names.
If you run MCPProxy: MCPProxy is not affected by CVE-2026-27896 due to its use of mark3labs/mcp-go and its architecture that does not rely on JSON field name inspection for security decisions. No action is required, but stay current with updates:
go install github.com/smart-mcp-proxy/mcpproxy-go/cmd/mcpproxy@latest
mcpproxy serveIf you are building any MCP tooling in Go: Add dec.DontMatchCaseInsensitiveStructFields() to every json.Decoder that processes untrusted input. Make it a linting rule. Make it a code review checkbox. The default behavior of encoding/json is a footgun for any security-sensitive application.
The MCP Security Posture Going Forward
Thirty CVEs in fifteen months is not a sign of a broken protocol. It is a sign of a protocol under active security scrutiny — which is exactly what should happen when a new standard gains rapid adoption. The alternative, zero CVEs, would mean nobody is looking.
But the acceleration is concerning. Fifteen CVEs in the last three months suggests that security researchers are finding a rich attack surface, and the rate of discovery is outpacing the rate of remediation. The MCP ecosystem needs to mature its security practices quickly: mandatory authentication, SDK-level input validation, gateway-level request normalization, and runtime isolation as a default rather than an option.
CVE-2026-27896 is a clean, well-understood vulnerability with a straightforward fix. The next one might not be. Build your defenses now, while the fixes are still simple.
For more on MCP security architecture, see our previous analysis of the MCP security landscape and what every gateway needs. MCPProxy is open source at github.com/smart-mcp-proxy/mcpproxy-go.